“Ransomware is more about manipulating vulnerabilities in human psychology than the adversary’s technological sophistication.” ― James Scott, Sr. Fellow, Institute for Critical Infrastructure Technology
We all dread the possibility that we turn our computer on and see the following message: “Your files are encrypted.” In simple words, it means “we got you, and unless you pay us a fee to release these files, you can say goodbye to them forever.”
That’s how ransomware works. It’s malware that you can accidentally download from a website or email attachment and, once it’s installed, it can take over your device and do whatever it wants. Whether you get ransomware on your personal computer or on your work computer, the risk can be huge (relative to the person or business).
Here is an example of what a ransomware message may look like:
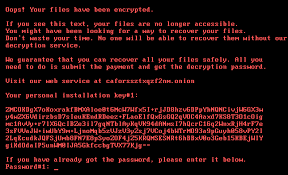
As scary as this looks, knowing the risks and how to prevent them will help you avoid being trapped in this type of situation.
Let’s examine the risks associated with ransomware and compare them between consumers and businesses:
Although hackers have more to gain from businesses, especially larger corporate enterprises in terms of pay, consumers have low-hanging fruit. This is because consumers are less sophisticated in security and have less information security resources than larger organizations. Thus, they are more likely to pay the ransom than corporations. In fact, in 2018, 39% of ransomware victims paid the ransom. In 2019, that number rose to 45%, and today, 58% of ransomware victims have paid the ransom.
The first and most significant risk for consumers is their lack of knowledge of ransomware. In fact, 45% of consumers don’t even know what ransomware is, and as many as 23% of consumers do not back up their files on their computer or mobile device.
Because of their lack of knowledge, consumers face the loss of data due to the ransomware and the loss of use of the device itself, and finally, the financial impact paying the ransom may incur, should they choose to pay.
Although consumers are the low-hanging fruit for ransomware hackers, there’s a clear shift in victims to businesses. In 2019 enterprises saw a 363% increase in ransomware attacks from the previous year, surpassing consumer attacks for the first time.
But why are these hackers targeting businesses all of a sudden? The reason is simple: they got a lot more to lose. While an ‘average Joe’ may lose his photographs (that are likely also stored on a cloud somewhere), a business’s data is much more precious, and losing it can put the entire company at stake.
The following are the business risks associated with ransomware attacks:
ZoneAlarm Extreme Security includes powerful zero-day protection features such as ZoneAlarm Anti-Ransomware, phishing protection, antivirus, and many other cybersecurity features. Thus, it contains everything you need to protect yourself or your business against the most sophisticated cyberattacks.
2. Use an Anti-Ransomware software
Should you wish to stay with your current antivirus program but want one of the most robust anti-ransomware software out there, ZoneAlarm Anti-Ransomware is your best bet. A PC Magazine Editor’s Choice award-winner, this product is a behavioral-based solution that doesn’t need to be connected to a network. It protects all the data on the device and not just a limited amount of data or a specific folder/s. Moreover, it doesn’t need any predefined settings— only 1 click to install and activate, and most importantly – restore any file that was encrypted during the attack automatically. It’s safe for consumers and businesses alike, as it was developed by Check Point, the enterprise cybersecurity global giant.
3. Backup your data
Opt to keep your files on a system separate from the network so that the ransomware won’t affect it too, such as an external hard drive. That way, if you do get a ransomware infection, you can erase your device and reinstall your files from backup. Although you may have access to your files by backing them up, hackers may still publish or sell that data, so prevention from the very start is key.
4. Exercise good judgment
Be careful when opening email attachments. Make sure the sender is real and trusted. Simply hover over the name or email address and see if you recognize it. Do not click any links or attachments in the email before confirming that the sender is known and real. It may say “Amazon,” but once you hover over it with the cursor, you may see a bizarre email address that you do not recognize. A quick Google search should tell you if the email address is standard or not.
5. Implement employee education programs (Business)
Provide regular security awareness training for employees to learn about possible cyber threats and how to avoid them.
6. Only use secure networks
Public Wi-Fi networks are easy for hackers to access. Instead, when in public, use a VPN that offers a secure internet connection.