Sextortion – a portmanteau of the words sex and extortion – is a broad term used to describe the practice of exploiting a person (usually in an attempt to get money) by threatening to reveal evidence of their sexual activity, often explicit photos or videos. Sextortion is not a new concept, and we can find evidence of the term being used as early as the 1950s. But the modern definition of sextortion is widely understood to be linked with exploitation through technology – email scams, webcam hacks, stolen photos and videos, etc. It is seen as a growing problem internationally, and it is another weapon that cybercriminals use to target us.
Example of Sextortion
Sextortion email scams have become particularly problematic in recent years. Scammers will send an email claiming to have evidence of the user in a compromising position, such as a video of the user viewing pornographic material. The scammers will post the user’s password as ‘evidence’ that they have access to the user’s device or files and will then demand a ransom. They threaten that is the ransom isn’t paid, they will release the video/photos to loved ones or colleagues.
In reality, though, it is often the case that the scammers have no such evidence of the user’s activity; they are just bluffing to get the user to pay the ransom. A password can be bought for a few dollars on the dark web, and scammers are often clever in how they present the little information they have. Moreover, they have the benefit of being able to send out huge numbers of emails. In 2019, for example, a report by Check Point uncovered that scammers were using the Phorpiex botnet to send out up 30,000 of these emails per hour. Each such scamming campaign can reach up to 27 million potential victims.
So, what does a typical sextortion email look like? As we mentioned, the scammers will usually try to grab your attention by putting your password (or another piece of personal information) prominently in the email; either in the top of the text or the email subject line. The scammer might introduce themselves like this:
Next will come the threat, coupled with any extra information they have on you:
And then, the demand for ransom:
…solution is to pay me $889. Let’s name it as a donation
The quotes above are taken from real sextortion emails reported by the media. While the emails often follow this pattern, there can be any number of variations.
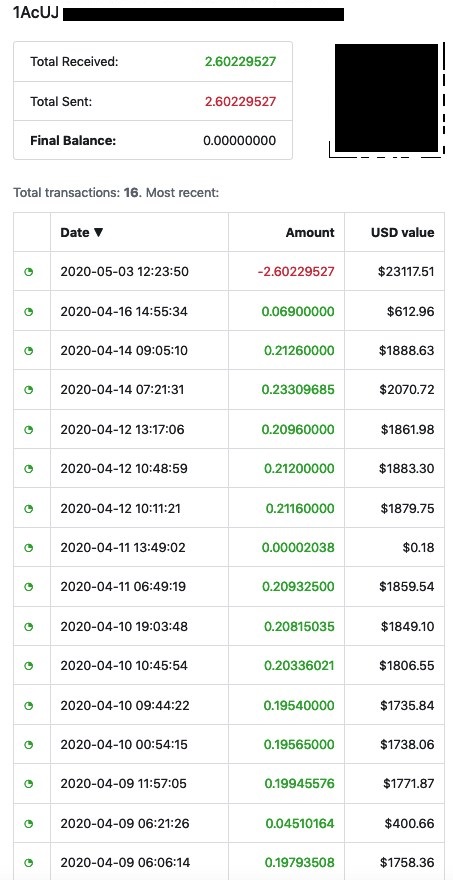
The scammers will often lead the victim to pay them using bitcoin using a link. Unfortunately, many fall victim to the trap. Here is an example of a Bitcoin wallet of a sextortion scammer:
What to do if you receive a sextortion email?
1. The first step is not to panic, and to not pay the ransom. Although they have your password, it is unlikely that they have access to your device. As we mentioned above, these scammers are more likely to be tricking you with psychology than they are to have real evidence of any such activity. They are aware that embarrassment over sexual activity plays into some of our worst fears, and they know that people might panic and pay – even if they have not done what the fraudulent email is suggesting. Scammers also know that embarrassment over sexual activity means you might be reluctant to report matters to the police or the management or security team in your workplace.
2. While remaining calm, next you should check the details of the password they have sent you. Is it an old password? Which accounts are linked with it? There are some password tools available online which allow you to check if your account details have been compromised such as this. Even if you do find some accounts have been compromised, you are just one of thousands of accounts getting these messages, and these hackers are simply waiting for someone to pay the ransom.
3. As in any kind of scam, you should report the problem to the relevant authorities – the police, the IT department in your office, security office of your university if you are a student, etc.
How to prevent sextortion emails
We have looked at how to react to a sextortion email scam, but it is arguably just as important to look at measures of prevention.
1. The first place you should start is with comprehensive anti-malware software protection, which should include robust anti-phishing capabilities, an important first line of defense. For example, if you install anti-phishing and anti-ransomware software as part of a ZoneAlarm solution such as ZoneAlarm Extreme Security for PC and mobile devices, emails are scanned for malware before they reach your inbox, and phishing-containing websites are prevented from allowing you to insert your credentials. Moreover, the software helps prevent identity theft, protecting your personal information including passwords and keystrokes.
2. There are also other practical steps you can take, such as using strong, different passwords for your accounts— and regularly updating them.
3. Whether an instance of sextortion or not, it’s good practice to report any phishing emails to your email provider. This has the dual effect of blocking future sextortion emails from the same account entering your email account and of making your email provider aware so they can take necessary steps.